I have been presenting the material from our book over the last several months and have been asked questions about some of the anti-patterns and how we avoid or solve them. Most recently at Web 2.0, I was talking with a bunch of smart, interesting people and a few things have bubbled up that I think are worth poking at that we need to pay attention to as “social” becomes more ubiquitous.
Issue 1: Authentication Service Hell
The first is the UI and conceptual quagmire we have inadvertently created through the pushing of OpenID. We (the large internet developer/designer We) have been pushing to protect people from the password anti-pattern and from ID/password fatigue. This is a good thing and we still have a ways to go to finally have people stop taking this shortcut. But, as a result we have OpenID, and have options from many different providers. And now we have Facebook Connect and Google Friend Connect and who knows how many other options will appear before it resolves into something understandable.
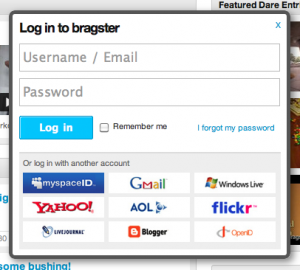
Now when I go onto a site, a site wanting to embrace open standards, a site committed to allowing their users to sign in with authentication credentials they already have, I am assaulted by a thousand logos and options, usually in addition to the ability to create a new account. Chris Messina, labels this the Nascar problem.
This new world is almost as bad as the problem it was trying to solve, especially for a less tech saavy person. The potential dangerous, security side effects are dealt with but the confusion and uncertainty of what is happening and how it all works still remains. I consider myself an early adopter and I am overwhelmed and don’t always remember my OpenID or other logins and it isn’t always clear how logging in with my Yahoo! ID on a non- Yahoo! site isn’t logging into Yahoo!
I am not clear on what the answer is, my team worked on the OpenID implementation at Yahoo! and we struggled for months with just the provisioning half of the equation. That said, I think we need to think long and hard about how we implement these solutions because in our effort to make things clearer and easier for our users we have created another, equally confusing (although safer) problem.
If you have ideas, there is an OpenID User Experience list for just this discussion. And it’s definitely a space that needs more design thought.
Issue 2: Location Hide and Seek
The second thing that I have been thinking about are all the applications launching for the phone that are utilizing the intersections between the social graph and the geo features. Lots and lots of cool things people are trying out and experimenting with which is fabulous and should yield new ways of thinking about self and location and devices. But from a safety consideration viewpoint, we are teaching people, especially young women, to share their whereabouts with everyone they know and sometimes don’t know, all the time. Can you say stalkers-r-us?
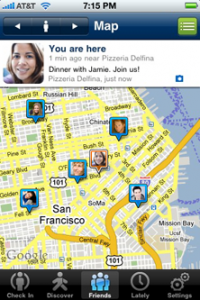
And from another aspect, we are also telling people when we are not at home. It’s only a matter of time before some tech saavy burglers figure this out and start ripping people off who are tweeting or foursquaring that they are in another state or across town or on vacation for awhile.
Not enough of these apps have enough security features and privacy filters built into them yet and if they do it’s not clear where they are and how to activate them when mobile. We spend a lot of time worrying about the phishers and the online scammers and even to some extent, online stalkers, but as soon as it moves into applications with offline capabilities, the stakes increase exponentially. I expect we will see more experimenting while audiences and adoption is small but once one of these apps becomes more popular and hits scale, these kinds of concerns will have to be addressed. It’s easier when to play with ideas when there isn’t scale.
It will be a fine balance between ease of use and providing functionality for users to be able to filter as they see appropriate. How granular is enough? When is it too much? We know people won’t/don’t go into preferences so considering the defaults that marry a nice balance between the needs of the business with the privacy and security concerns of the people becomes even more important for consideration.
1 Comment
Comments are closed.